-
Important Announcement for the TrueNAS Community.
The TrueNAS Community has now been moved. This forum will now become READ-ONLY for historical purposes. Please feel free to join us on the new TrueNAS Community Forums
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
Nextcloud Iocage and PfSense
- Thread starter nic_greene
- Start date
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
@Jailer Thank you.Yes.
Is the other rule ok?
And do I need to setup any other rules for this IP, like in the LAN?
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
@Jailer Thank you. So you are saying I don't need to create any rules within the LAN Tab of Firewall/Rules?The rules should be created automatically for each port forward.
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
With the NAT Rules setup, the only thing missing was this in the DNS Resolver
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
No. It's coming from Route 53. Actually got the mapping from Sam Dowlings Reverse Proxy Tut. Thanks @KevDog, I now have a working pfsense setup.So is your reverse proxy running on same VM as Nextcloud?
@nic_greene
I'm glad you got it running OK. I don't use AWS at all -- am interested in trying it. What are you hosting there other than a reverse proxy?
One thing you might want to consider. Sam Dowling's tutorial describes a reverse proxy but I correct me if I'm wrong I think all of his stuff is running on AWS. Is your reverse proxy and nextcloud located on different physical machines?
I'm glad you got it running OK. I don't use AWS at all -- am interested in trying it. What are you hosting there other than a reverse proxy?
One thing you might want to consider. Sam Dowling's tutorial describes a reverse proxy but I correct me if I'm wrong I think all of his stuff is running on AWS. Is your reverse proxy and nextcloud located on different physical machines?
Jailer
Not strong, but bad
- Joined
- Sep 12, 2014
- Messages
- 4,977
Dude, the reverse proxy is on Route 53 (he's said that at least 3 times in this thread) and points to his public IP. It's then forwarded to his jail via the port forward and host override he added above.
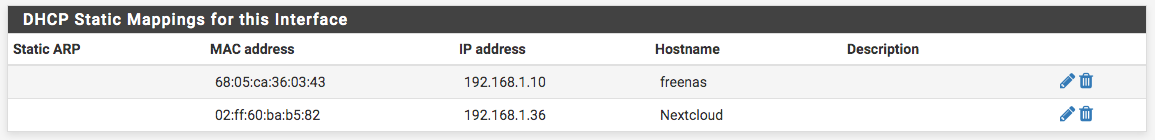
And @nic_greene your static IP's on your LAN won't show up in your DHCP lease page unless you add a static mapping since it's not a DHCP lease.
And @nic_greene your static IP's on your LAN won't show up in your DHCP lease page unless you add a static mapping since it's not a DHCP lease.
danb35
Hall of Famer
- Joined
- Aug 16, 2011
- Messages
- 15,504
It's possible that some of the confusion stems from wondering why he'd do that--I don't see the point in running a reverse proxy remotely that just proxies to resources on your LAN. Particularly when pfSense is perfectly capable of handling this itself.Dude, the reverse proxy is on Route 53 (he's said that at least 3 times in this thread) and points to his public IP.
@Jailer -- however the reverse proxy instructions he's following makes an unencrypted http connection to the backend -- so why I wanted to ensure that if the rev proxy was on AWS and his pfsense/freenas/nextcloud was at home or another LAN -- then the reverse proxy would be proxying to unencrypted to remote sources. Hence me asking all the questions like a million times.
And unrelated -- why does nginx called backend servers "upstream"? That doesn't make a lot of sense to me!
And unrelated -- why does nginx called backend servers "upstream"? That doesn't make a lot of sense to me!
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
@danb35 Yes, I use Route 53 to route traffic to my nextcloud and other sites/servers.
All of the traffic thru Route 53 is encrypted, used the hardened Nextcloud guide from @samuel-emrys here
@Jailer the Static Routes are now all working with static mapping, I managed to muddle through that with everyone's help
All of the traffic thru Route 53 is encrypted, used the hardened Nextcloud guide from @samuel-emrys here
@Jailer the Static Routes are now all working with static mapping, I managed to muddle through that with everyone's help
samuel-emrys
Contributor
- Joined
- Dec 14, 2018
- Messages
- 136
I think there might be some confusion here. All of the services I have run locally on my LAN, hosted in FreeNAS iocage jails. I don't run anything on AWS. The only reason I use Route 53 is to make my local services publicly routable, which is convenient because my _website_ is hosted using AWS.No. It's coming from Route 53. Actually got the mapping from Sam Dowlings Reverse Proxy Tut. Thanks @KevDog, I now have a working pfsense setup.
The reverse proxy I've configured runs on my LAN. The rules I specify forward traffic to the reverse proxy jail, which forwards traffic to whichever service is being requested, in your case this is Nextcloud. This means that the rules I've specified won't necessarily apply to you if you've got a different configuration.
As far as your nextcloud instance showing up in pfSense goes, what's happening at the moment makes sense because the instructions I provide include a manual IP configuration. The manual IP I set is outside of my DHCP range, and I've added an alias for each service so that I can easily identify them when creating rules. Having said that, if you _want_ it to show up in your DHCP Leases/ARP table, adding a static mapping or any of the alternatives @danb35 suggested earlier would be appropriate. If you want the jail to draw a DHCP address though, you'll need to configure it that way. I normally just map these statically by IP instead of MAC.
Also a bit of a semantic point, but note that traffic doesn't go "through" Route 53 - It provides domain name system (DNS) resolution. All it is is a mapping of your website URL with your public IP. i.e., if you have three services, Nextcloud, Bitwarden, Heimdall, all hosted on a server on your home network, and your public IP address is 15.15.15.15, then you might create the equivalent of the following mappings in Route 53:
| Service | Route 53 <url:ip> mapping |
| nextcloud | <cloud.example.com:15.15.15.15> |
| bitwarden | <bitwarden.example.com:15:15:15.15> |
| heimdall | <heimdall.example.com:15.15.15.15> |
You can confirm this by running
nslookup from a computer not connected to your LAN (if you have a local mapping for the service subdomains, as I detail in my guide, otherwise it should work from inside your LAN as well), which should show something similar to the following:Code:
$ nslookup cloud.example.com Server: 8.8.8.8 Address: 8.8.8.8#53 Non-authoritative answer: Name: cloud.example.com Address: 15.15.15.15
With this in mind, @KevDog makes a valid point. If your reverse proxy is hosted on AWS (in an EC2/Elastic Beanstalk instance or similar) then the configuration I've provided won't be suitable since it makes unencrypted connections to the services. It's only encrypted from the reverse proxy onwards. This means that if you have locally hosted servers and your reverse proxy on AWS, then all of the traffic between your house and the AWS servers will be unencrypted. Not good.
Last edited:
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
@samuel-emrys Thanks for the very detailed explanation/clarification.
My nextcloud instance is setup following your guide. The only difference, presently, is that I have not set up the nginx reverse proxy in jail, as per your more recent guide. I plan to do this.
The situation I ran into, that prompted this post, was twofold: manual ip configuration in pfsense and how to get my nextcloud instance, on my local server, to be available via it's domain name. I had setup a box to run pfsense with aes-ni so I could use open vpn to tend to my network remotely, as well as being able to delve into better network security practices. I was upgrading from a Netgear Router which had limited capabilities and a very different way of handling manual ip entries.
As you point out route 53 is acting only for DNS resolution, so apologies for being ambiguous in my communication, but as it does follow your guide all traffic is encrypted and I've had this instance running for 9+ months now with very minor hiccups.
Thanks to all the forum users @KevDog, @Jailer, @danb35, @Apollo who obviously scratched their heads on what I was on about, whilst helping me get this sorted out.
@samuel-emrys I appreciate your guides because you 1) explain what is going on in simple terms, which is very helpful for someone like me and 2) are very willing to help out with bugs etc.,
I'd really be grateful for any input on SIMPLE guides to pfsense - but maybe what I am lacking is a basic primer on Networking and best practices because what I posted was initially confusing to other users.
My nextcloud instance is setup following your guide. The only difference, presently, is that I have not set up the nginx reverse proxy in jail, as per your more recent guide. I plan to do this.
The situation I ran into, that prompted this post, was twofold: manual ip configuration in pfsense and how to get my nextcloud instance, on my local server, to be available via it's domain name. I had setup a box to run pfsense with aes-ni so I could use open vpn to tend to my network remotely, as well as being able to delve into better network security practices. I was upgrading from a Netgear Router which had limited capabilities and a very different way of handling manual ip entries.
As you point out route 53 is acting only for DNS resolution, so apologies for being ambiguous in my communication, but as it does follow your guide all traffic is encrypted and I've had this instance running for 9+ months now with very minor hiccups.
Thanks to all the forum users @KevDog, @Jailer, @danb35, @Apollo who obviously scratched their heads on what I was on about, whilst helping me get this sorted out.
@samuel-emrys I appreciate your guides because you 1) explain what is going on in simple terms, which is very helpful for someone like me and 2) are very willing to help out with bugs etc.,
I'd really be grateful for any input on SIMPLE guides to pfsense - but maybe what I am lacking is a basic primer on Networking and best practices because what I posted was initially confusing to other users.
nic_greene
Dabbler
- Joined
- Sep 5, 2015
- Messages
- 41
Maybe I spoke to soon:
Getting this message in my freenas box: Feb 15 07:33:55 freenas dhclient[36403]: send_packet: No buffer space available
What does that mean? Better yet, what do I do about it?
Getting this message in my freenas box: Feb 15 07:33:55 freenas dhclient[36403]: send_packet: No buffer space available
What does that mean? Better yet, what do I do about it?
Similar threads
- Replies
- 3
- Views
- 5K
- Replies
- 2
- Views
- 5K
- Replies
- 11
- Views
- 2K
