-
Important Announcement for the TrueNAS Community.
The TrueNAS Community has now been moved. This forum will now become READ-ONLY for historical purposes. Please feel free to join us on the new TrueNAS Community Forums
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
SOLVED Updating to RC1 AD problem
- Thread starter Elo
- Start date
- Joined
- Mar 6, 2014
- Messages
- 9,554
You can look in /var/log/middlewared.log for exact reason for failure. I recently noticed a couple of users had failures in activedirectory.change_trust_pw. I added a fix for this to go into 11.3-RELEASE. change_trust_pw is called because of some changes to simplify setup / configuration of kerberized NFS in AD environments.
hi anodos...
I only find lines like :
[2019/11/28 09:41:12] (DEBUG) common.freenasldap.get_SRV_records():1142 - FreeNAS_ActiveDirectory_Base.get_SRV_records: looking up SRV records for _ldap._tcp.xxxxx.yyyyyy.com
Which does not shred any light on the problem for me.
i am able to ping it thrugh ist virtual adress so the IP is resolved. I am not allowed to connect to it through the explorer on the server 2016.
I shold mention that i did two things at the same time:
1. upgrade to RC1
2. change the mb to a supermicro board.
I have another FreeNas server which after upgradeto RC1 WORKS just fine?
You can look in /var/log/middlewared.log for exact reason for failure. I recently noticed a couple of users had failures in activedirectory.change_trust_pw. I added a fix for this to go into 11.3-RELEASE. change_trust_pw is called because of some changes to simplify setup / configuration of kerberized NFS in AD environments.
I only find lines like :
[2019/11/28 09:41:12] (DEBUG) common.freenasldap.get_SRV_records():1142 - FreeNAS_ActiveDirectory_Base.get_SRV_records: looking up SRV records for _ldap._tcp.xxxxx.yyyyyy.com
Which does not shred any light on the problem for me.
i am able to ping it thrugh ist virtual adress so the IP is resolved. I am not allowed to connect to it through the explorer on the server 2016.
I shold mention that i did two things at the same time:
1. upgrade to RC1
2. change the mb to a supermicro board.
I have another FreeNas server which after upgradeto RC1 WORKS just fine?
- Joined
- Mar 6, 2014
- Messages
- 9,554
Leave AD on the machine:hi anodos...
I only find lines like :
[2019/11/28 09:41:12] (DEBUG) common.freenasldap.get_SRV_records():1142 - FreeNAS_ActiveDirectory_Base.get_SRV_records: looking up SRV records for _ldap._tcp.xxxxx.yyyyyy.com
Which does not shred any light on the problem for me.
i am able to ping it thrugh ist virtual address so the IP is resolved. I am not allowed to connect to it through the explorer on the server 2016.
I shold mention that i did two things at the same time:
1. upgrade to RC1
2. change the mb to a supermicro board.
I have another FreeNas server which after upgradeto RC1 WORKS just fine?
midclt call activedirectory.leave '{"username": "your AD service account", "password": "your password"}'. This command (if it succeeds) will clear the relevant config for your AD domain. Once you have done this, retry with the webui and check contents of "/var/log/middlewared.log". This time check the verbose logging checkbox in the webui.Leave AD on the machine:midclt call activedirectory.leave '{"username": "your AD service account", "password": "your password"}'. This command (if it succeeds) will clear the relevant config for your AD domain. Once you have done this, retry with the webui and check contents of "/var/log/middlewared.log". This time check the verbose logging checkbox in the webui.
Can't find much info on this command. to be clear if i understand correctly:
1. first username is user on Freenas or the user used to access the share
2. ad service account is the user on the ad server
3. password is the password of the ad service account
4. your password is the freenas user password or password for the share
???
Last edited:
- Joined
- Mar 6, 2014
- Messages
- 9,554
It should be an appropriately-privileged AD service account. The credentials (assuming that AD is in a working state) will be used to kinit, and then the resulting kerberos ticket used to perform "net -k ads leave". Once this is complete, it will kdestroy, and remove kerberos config. This is a relatively clean state from which to perform a fresh AD join.
Whit ole_berg beeing the my user on my Domain ... (login user on W10 machines in the domain also accessing the data shares both from FreeNAS servers and Windows servers)
For AD service account user I used the user that is defined in the AD setup on FreeNAS. But something is not corrects:
[ole_berg] Field was not expected
Traceback (most recent call last):
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 128, in call_method
result = await self.middleware.call_method(self, message)
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 1113, in call_method
return await self._call(message['method'], serviceobj, methodobj, params, app=app, io_thread=False)
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 1061, in _call
return await methodobj(*args)
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 948, in nf
args, kwargs = clean_and_validate_args(args, kwargs)
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 906, in clean_and_validate_args
value = attr.clean(args[args_index + i])
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 588, in clean
raise Error(key, 'Field was not expected')
middlewared.schema.Error: [ole_berg] Field was not expected
For AD service account user I used the user that is defined in the AD setup on FreeNAS. But something is not corrects:
[ole_berg] Field was not expected
Traceback (most recent call last):
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 128, in call_method
result = await self.middleware.call_method(self, message)
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 1113, in call_method
return await self._call(message['method'], serviceobj, methodobj, params, app=app, io_thread=False)
File "/usr/local/lib/python3.7/site-packages/middlewared/main.py", line 1061, in _call
return await methodobj(*args)
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 948, in nf
args, kwargs = clean_and_validate_args(args, kwargs)
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 906, in clean_and_validate_args
value = attr.clean(args[args_index + i])
File "/usr/local/lib/python3.7/site-packages/middlewared/schema.py", line 588, in clean
raise Error(key, 'Field was not expected')
middlewared.schema.Error: [ole_berg] Field was not expected
- Joined
- Mar 6, 2014
- Messages
- 9,554
Not a problem. We're adding that to the UI for the actual release (a button to leave the AD domain). The gist of what I want you to do is simple: cleanly leave AD, remove kerberos realm and keytab from UI, destroy kerberos ticket, and restart from clean state with logging turned up. Then check the middlewared.log.Embarrassing... I will try that when home. Thanks and will report back for others if they have samme problem.. /O
I am afraid this did not work, that is that leaving the domain resturns NUL and ok in the log but joining..... Here are the last lines:
ads_dc_name: using server='OB-MSSERVER2016.HJEMME.VABRAATEN95.COM' IP=192.168.111.36
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
ads_dc_name: domain=HJEMME
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
name HJEMME.VABRAATEN95.COM#1C found.
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:389
ads_try_connect: sending CLDAP request to 192.168.111.36 (realm: HJEMME.VABRAATEN95.COM)
Successfully contacted LDAP server 192.168.111.36
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
resolve_ads: Attempting to resolve KDCs for HJEMME.VABRAATEN95.COM using DNS
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:88
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
resolve_ads: Attempting to resolve KDCs for HJEMME.VABRAATEN95.COM using DNS
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:88
create_local_private_krb5_conf_for_domain: wrote file /var/run/samba4/smb_krb5/krb5.conf.HJEMME with realm HJEMME.VABRAATEN95.COM KDC list =
ads_dc_name: using server='OB-MSSERVER2016.HJEMME.VABRAATEN95.COM' IP=192.168.111.36
ads_try_connect: sending CLDAP request to 192.168.111.36 (realm: HJEMME.VABRAATEN95.COM)
Successfully contacted LDAP server 192.168.111.36
Connected to LDAP server OB-MSSERVER2016.hjemme.vabraaten95.com
KDC time offset is 0 seconds
Found SASL mechanism GSS-SPNEGO
ads_sasl_spnego_bind: got OID=1.3.6.1.4.1.311.2.2.30
ads_sasl_spnego_bind: got OID=1.2.840.48018.1.2.2
ads_sasl_spnego_bind: got OID=1.2.840.113554.1.2.2
ads_sasl_spnego_bind: got OID=1.2.840.113554.1.2.2.3
ads_sasl_spnego_bind: got OID=1.3.6.1.4.1.311.2.2.10
GENSEC backend 'gssapi_spnego' registered
GENSEC backend 'gssapi_krb5' registered
GENSEC backend 'gssapi_krb5_sasl' registered
GENSEC backend 'spnego' registered
GENSEC backend 'schannel' registered
GENSEC backend 'naclrpc_as_system' registered
GENSEC backend 'sasl-EXTERNAL' registered
GENSEC backend 'ntlmssp' registered
GENSEC backend 'ntlmssp_resume_ccache' registered
GENSEC backend 'http_basic' registered
GENSEC backend 'http_ntlm' registered
GENSEC backend 'http_negotiate' registered
Starting GENSEC mechanism spnego
Starting GENSEC submechanism gse_krb5
smb_gss_krb5_import_cred ccache[MEMORY:net_ads] failed with [ Miscellaneous failure (see text): unknown mech-code 2 for mech 1 2 840 113554 1 2 2] -t
Failed to start GENSEC client mech gse_krb5: NT_STATUS_INTERNAL_ERROR
gensec_spnego_create_negTokenInit_step: Failed to setup SPNEGO negTokenInit request
gensec_update_done: spnego[0x814c15f60]: NT_STATUS_INVALID_PARAMETER
ads_sasl_spnego_gensec_bind(KRB5) failed for ldap/ob-msserver2016.hjemme.vabraaten95.com with user[OB-NAS-MAIN$] realm=[HJEMME.VABRAATEN95.COM]: Cann
Join to domain is not valid: NT code 0xfffffff6
return code = -1]
[2019/12/29 18:04:24] (DEBUG) ActiveDirectoryService.start():969 - Test join to HJEMME.VABRAATEN95.COM failed. Performing domain join.
[2019/12/29 18:04:28] (DEBUG) ActiveDirectoryService.start():987 - Successfully generated keytab for computer account. Clearing bind credentials
[2019/12/29 18:04:28] (DEBUG) ServiceService._simplecmd():286 - Calling: restart(cifs)
[2019/12/29 18:04:28] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/smb4.conf
[2019/12/29 18:04:28] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/smb4_share.conf
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/pop3
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/xdm
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/pam.inc
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/atrun
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/other
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/cron
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/telnetd
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/kde
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/sudo
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/README
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/imap
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/rsh
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/system
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/system
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/passwd
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/nslcd.conf
ads_dc_name: using server='OB-MSSERVER2016.HJEMME.VABRAATEN95.COM' IP=192.168.111.36
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
ads_dc_name: domain=HJEMME
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
name HJEMME.VABRAATEN95.COM#1C found.
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:389
ads_try_connect: sending CLDAP request to 192.168.111.36 (realm: HJEMME.VABRAATEN95.COM)
Successfully contacted LDAP server 192.168.111.36
sitename_fetch: Returning sitename for realm 'HJEMME.VABRAATEN95.COM': "Default-First-Site-Name"
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
resolve_ads: Attempting to resolve KDCs for HJEMME.VABRAATEN95.COM using DNS
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:88
saf_fetch: failed to find server for "HJEMME.VABRAATEN95.COM" domain
get_dc_list: preferred server list: ", *"
resolve_ads: Attempting to resolve KDCs for HJEMME.VABRAATEN95.COM using DNS
get_dc_list: returning 1 ip addresses in an ordered list
get_dc_list: 192.168.111.36:88
create_local_private_krb5_conf_for_domain: wrote file /var/run/samba4/smb_krb5/krb5.conf.HJEMME with realm HJEMME.VABRAATEN95.COM KDC list =
ads_dc_name: using server='OB-MSSERVER2016.HJEMME.VABRAATEN95.COM' IP=192.168.111.36
ads_try_connect: sending CLDAP request to 192.168.111.36 (realm: HJEMME.VABRAATEN95.COM)
Successfully contacted LDAP server 192.168.111.36
Connected to LDAP server OB-MSSERVER2016.hjemme.vabraaten95.com
KDC time offset is 0 seconds
Found SASL mechanism GSS-SPNEGO
ads_sasl_spnego_bind: got OID=1.3.6.1.4.1.311.2.2.30
ads_sasl_spnego_bind: got OID=1.2.840.48018.1.2.2
ads_sasl_spnego_bind: got OID=1.2.840.113554.1.2.2
ads_sasl_spnego_bind: got OID=1.2.840.113554.1.2.2.3
ads_sasl_spnego_bind: got OID=1.3.6.1.4.1.311.2.2.10
GENSEC backend 'gssapi_spnego' registered
GENSEC backend 'gssapi_krb5' registered
GENSEC backend 'gssapi_krb5_sasl' registered
GENSEC backend 'spnego' registered
GENSEC backend 'schannel' registered
GENSEC backend 'naclrpc_as_system' registered
GENSEC backend 'sasl-EXTERNAL' registered
GENSEC backend 'ntlmssp' registered
GENSEC backend 'ntlmssp_resume_ccache' registered
GENSEC backend 'http_basic' registered
GENSEC backend 'http_ntlm' registered
GENSEC backend 'http_negotiate' registered
Starting GENSEC mechanism spnego
Starting GENSEC submechanism gse_krb5
smb_gss_krb5_import_cred ccache[MEMORY:net_ads] failed with [ Miscellaneous failure (see text): unknown mech-code 2 for mech 1 2 840 113554 1 2 2] -t
Failed to start GENSEC client mech gse_krb5: NT_STATUS_INTERNAL_ERROR
gensec_spnego_create_negTokenInit_step: Failed to setup SPNEGO negTokenInit request
gensec_update_done: spnego[0x814c15f60]: NT_STATUS_INVALID_PARAMETER
ads_sasl_spnego_gensec_bind(KRB5) failed for ldap/ob-msserver2016.hjemme.vabraaten95.com with user[OB-NAS-MAIN$] realm=[HJEMME.VABRAATEN95.COM]: Cann
Join to domain is not valid: NT code 0xfffffff6
return code = -1]
[2019/12/29 18:04:24] (DEBUG) ActiveDirectoryService.start():969 - Test join to HJEMME.VABRAATEN95.COM failed. Performing domain join.
[2019/12/29 18:04:28] (DEBUG) ActiveDirectoryService.start():987 - Successfully generated keytab for computer account. Clearing bind credentials
[2019/12/29 18:04:28] (DEBUG) ServiceService._simplecmd():286 - Calling: restart(cifs)
[2019/12/29 18:04:28] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/smb4.conf
[2019/12/29 18:04:28] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/smb4_share.conf
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/pop3
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/xdm
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/pam.inc
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/atrun
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/other
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/cron
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/telnetd
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/kde
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/sudo
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/README
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/imap
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/rsh
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/system
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/system
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/pam.d/passwd
[2019/12/29 18:04:30] (DEBUG) EtcService.generate():274 - No new changes for /etc/local/nslcd.conf
Those log messages indicate that a testjoin failed (expected), then a proper AD join succeeded. AD should be working. Does "wbinfo -t" return correctly?
Yes it does....
But when attempting to access the FreeNAS server via Windows explorer and SMB shares the server does not allow connection:
\\OB-NAS-MAIN is not accessible. You might not have permission to use this network resource. Contact the administrator ...etc...etc..
There is nothing changed from a situation when this worked except that Motherboard of the FreeNAS server has been changed.
I am attempting to connect from the server that host the ADC.
It must be something related to authorization method but I can not find what... I have tried to adjust the ACL's but no luck..only permission denied!
Last edited:
- Joined
- Mar 6, 2014
- Messages
- 9,554
This means you probably have a permissions issue and not an AD issue. Post the ACL for each path component leading to your share.Yes it does....
But when attempting to access the FreeNAS server via Windows explorer and SMB shares the server does not allow connection:
\\OB-NAS-MAIN is not accessible. You might not have permission to use this network resource. Contact the administrator ...etc...etc..
There is nothing changed from a situation when this worked except that Motherboard of the FreeNAS server has been changed.
I am attempting to connect from the server that host the ADC.
It must be something related to authorization method but I can not find what... I have tried to adjust the ACL's but no luck..only permission denied!
Just saw you last post and i will post the ACL settings!
Hi Anodos... I have tested this further. I have two FreeNAS servers and I have upgraded both to RC1 .. I have used the new ACL editor to change the permissions on different shares and the results are not consistent. Two shares with exactely the same permissions behaves differently. Seems to be dependent on the permissions set when I did the upgrade. One is accessible from Windows Explorer and anothe one with similar permissions is not accessible (with error message similar to the one in the previous post). (Both on the same FreeNAS server and attempted accessed from the my Server 2016 machine). All permissions when canhged is changed recurively. I have also noticed that I am not allowed to use CHMOD from CLI in a SSH session (as root). This might be intentional but i find it a little strange.
I am not able to debug this further so please advice....
Those log messages indicate that a testjoin failed (expected), then a proper AD join succeeded. AD should be working. Does "wbinfo -t" return correctly?
Hi Anodos... I have tested this further. I have two FreeNAS servers and I have upgraded both to RC1 .. I have used the new ACL editor to change the permissions on different shares and the results are not consistent. Two shares with exactely the same permissions behaves differently. Seems to be dependent on the permissions set when I did the upgrade. One is accessible from Windows Explorer and anothe one with similar permissions is not accessible (with error message similar to the one in the previous post). (Both on the same FreeNAS server and attempted accessed from the my Server 2016 machine). All permissions when canhged is changed recurively. I have also noticed that I am not allowed to use CHMOD from CLI in a SSH session (as root). This might be intentional but i find it a little strange.
I am not able to debug this further so please advice....
- Joined
- Mar 6, 2014
- Messages
- 9,554
Ability to change permissions via chmod is controlled by the ZFS "aclmode" property on the underlying dataset. You can use the dataset editor in the UI to change the value of the parameter, but generally it's recommended to leave it on "restricted" which prevents chmod().
- Joined
- Mar 6, 2014
- Messages
- 9,554
One other item to bear in mind is that e(x)ecute for your user is required on all path components leading to a share.
If your share is /mnt/tank/foo/bar, then you need execute on /mnt/tank, /mnt/tank/foo, and /mnt/tank/foo/bar in order to access the contents of the share.
The permissions required to traverse to a share can be added by selecting the BASIC - TRAVERSE in the ACL editor.
If your share is /mnt/tank/foo/bar, then you need execute on /mnt/tank, /mnt/tank/foo, and /mnt/tank/foo/bar in order to access the contents of the share.
The permissions required to traverse to a share can be added by selecting the BASIC - TRAVERSE in the ACL editor.
This means you probably have a permissions issue and not an AD issue. Post the ACL for each path component leading to your share.
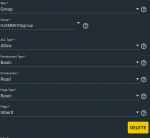
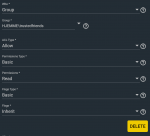
Please find attached info om ACLs for the VIDEO share.
Attachments
How is BASIC Traverse vs BASIC Full Control? Are they individualy exclusive or must both be added (for the owner)?One other item to bear in mind is that e(x)ecute for your user is required on all path components leading to a share.
If your share is /mnt/tank/foo/bar, then you need execute on /mnt/tank, /mnt/tank/foo, and /mnt/tank/foo/bar in order to access the contents of the share.
The permissions required to traverse to a share can be added by selecting the BASIC - TRAVERSE in the ACL editor.
Can't find out since the ACL Permissions list is not yet available)
- Joined
- Mar 6, 2014
- Messages
- 9,554
TRAVERSE = permission to click through a directoryHow is BASIC Traverse vs BASIC Full Control? Are they individualy exclusive or must both be added (for the owner)?
Can't find out since the ACL Permissions list is not yet available)
READ = TRAVERSE + permissions to read data, xattrs, etc
MODIFY = READ + permissions to write data, xattrs, etc (excluding change owner and write ACL)
FULL_CONTROL = MODIFY + permission to change owner and write ACL.
Post output of "getfacl /mnt/Pool_2", "getfacl /mnt/Pool_2/VIDEO", and "testparm -s".
Similar threads
- Locked
- Replies
- 11
- Views
- 5K
- Replies
- 5
- Views
- 2K
D