For what it's worth, i know this is an old thread, but in case someone later tries to figure this out.
It's possible to get this to work on TrueNAS scale, but it's a pill, and required a lot of debugging of winbindd to figure out what was going on.
1. The default LDAP configuration it makes is wrong if you use SSL. It still tries to use starttls. Easiest way around this is to set everything to use start tls rather than SSL.
2. Samba now requires write access to one of the main DN's. So you need to have it use a directory manager user so it can verify the ID pool.
3. ipa-adtrust-install needs to be run on the servers.
4. cifs keytab needs to be created with a machine password (see
https://freeipa.readthedocs.io/en/latest/designs/adtrust/samba-domain-member.html)
5. place cifs, keytab in /root/samba-keytab
6. SID needs to be set right (follow the guide above)
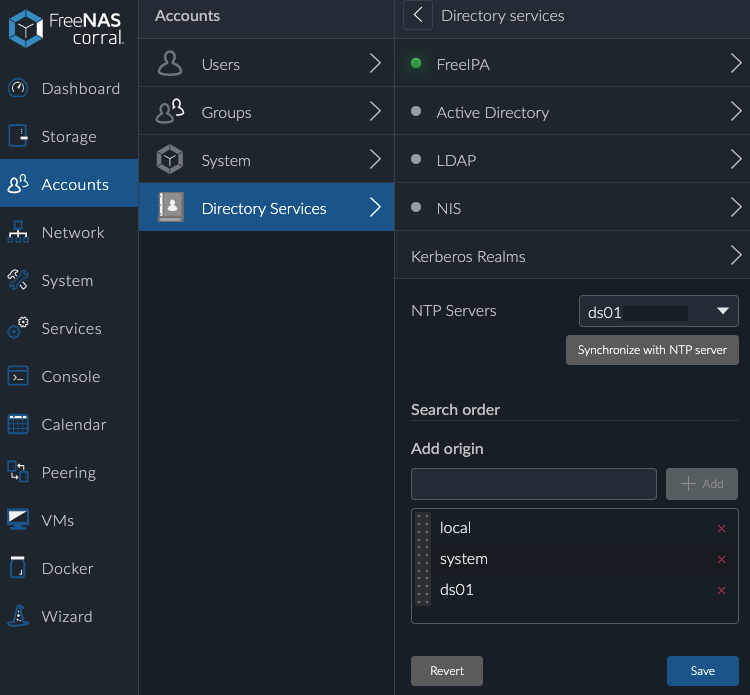
7. Aux parameters in truenas need to be set to enable the keytab/etc
Use:
dedicated keytab file = FILE:/root/samba-keytab/samba.keytab
kerberos method = dedicated keytab
server role = member server
realm = IPA REALM NAME (IE SERVERS.DBERLIN.ORG or whatever)
Note that your aux parameters will get overwritten in the registry if you touch the directory services config. So if you do that, you need to go back to the service config and re-save it so it re-adds the aux parameters to the registry.
You can use samba-regedit to verify your parameters are there (HKLM\Software\Samba\smbconf)
Lastly, you need to set the machine password.
The guide has directions. The db is in /var/db/system/samba rather than /var/lib/samba.
Once you do all that, restart the winbind and smb servers, and authentication using ipa users should work.
Honestly, after making it work, i think i would just move to AD.