@Shrdlu
When you speak of SSL being built in -- I don't know what that means. Why I say that is because for your domain you need proper SSL certs issued by a CA. A very popular SSL certificate agency used here in the forums and elsewhere is Lets Encrypt since they will allow you to obtain proper SSL certs for your domain for free.
You can use DuckDNS however I'll bet that its possible you can use the dynamic updater client built into FreeNAS or your router if you prefer another option.
As a side note and take this only as a recommendation -- I'm assuming you have your only personal domain name rather than a free domain as offered by no-ip.com or another service. I use Cloudflare as my domain name resolver (DNS resolver). Cloudflare is free and in addition it integrates really well with acme and Let's Encrypt in the process of obtaining and renewing your SSL certs. It's an option however it's very flexible
In terms of setting up Nextcloud -- don't use the plugin jail. I'm aware
@danb35 has a script in these forums how to setup nextcloud and many users have setup Nextcloud in this manner with success. In setting up my Nextcloud jail I used the instructions from this website:
https://www.samueldowling.com/2018/...n-freenas-iocage-jail-with-hardened-security/
I thought the installation steps were well explained and I learned a lot about setting up things. This guide unfortunately uses aws53 for its DNS resolver however the steps are similar for cloudflare -- you might have to google those. In addition
@danb35 has another script that allows for acme to be run as a cron job to automate cert renewals. One of the downsides of using Let's Encrypt is although the certs are free, they need to be renewed every 3 months. It's probably best to automate this process unless you are really good at remembering things in a timely manner (two qualities I lack).
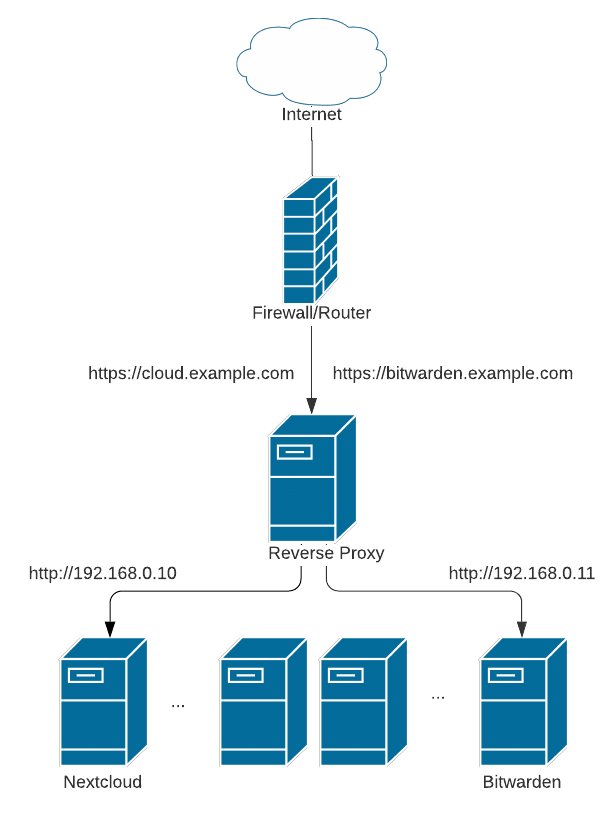
Each jail doesn't specifically need its own SSL cert -- you could set it up this way however that's two locations with certs that you'll need to remember to update. Another alternative is to set up one reverse proxy where all the certs are managed and then the reverse proxy would handle the SSL authentication and then proxy or forward the connection to the appropriate virtual host on the back end. The proxy could forward to your Plex setup and also forward to your Nextcloud setup. The certificates for your Plex and Nextcloud could be both installed and kept on the jail running your reverse proxy. Additional jails could then be setup to run plex and nextcloud.
There are unfortunately many ways to skin the cat. It just depends what you want to do. I can't say one setup is necessarily better or worse than another -- it's just a setup you think is easy to maintain and utilize. I like the jail-reverse proxy setup since all you need to do is open 80 or just 443 on your router to expose (if you need external access) so its just one entry point you need to manage. It's possible however to do it other ways. Here's another read for you about reverse proxies in case this concept is new to you:
Use an nginx reverse proxy to make multiple self hosted services available on your LAN and the internet using LetsEncrypt wildcard certificates for HTTPS
www.samueldowling.com