I agree with steps/ways mentioned here (use non-standard port, disable root logging and use "sudo" instead, use key instead of password, use VPN, ... etc). The thing is, that everything will leave the system "visible" from the other side.
- Changing of the port will eliminate most of the bots checking 22port only, but some bots are scanning several ports or port ranges. Also lot of bots/programs are able to detect what kind of service is running on that port.
- Direct approach mostly begining with full port range scan (1-65565) so soon or later it will "find" open SSH port (if there is one)
- Strong password will increase the time of the brute-force cracking to be successful but if someone wants to launch dictionary or brute-force attack on your IP, then he could initiate parallel attack to speed up the process (like hundred or thousand tries each time, or even more if the attacker will use BotNet). Without proper anti-hammering protection (and even with it in case of botnet) on the system (or before), he could be successful.
- Using RSA keys instead of password is very good choice. It is strong protection against the pwd cracking but it will not protect the system against SSH lockout. Thing is that there is limitation how many ssh communication threads can be active in one way. If the attacker will keep sending thousand of the requests, even the authorized person could be unable to connect because of this. Also authorization-check process is more consuming than simple packet dropping.
So, there is a way how to add another layer of protection -> Let the system "disappear" by closing all of the ports out of the local network. But how to open port from outside and connect in case of need?
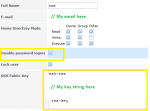
Port knocking is the nice and easy way how to achieve this. The way how it works is very simple. It is "listening" on specific ports and if it detect specific activity on specific ports in specific order in specific time-frame ( :D ), it will open the port for that host who properly "knocked on the door".
Example:
-> SYN packet
--> On ports 2222, 45841, 3178, 3128, 12785 in this order exactly
---> In time frame 10sec
----> Will open port 20202 which is the SSH port for system
-----> For the IP from which the knocking come
------> for 5 hours, or until "closure" knocking sequence is received
Technically it works like this:
1] Firewall rule which will block any communication on port 20202
2] Knock daemon is silently listening incoming communication on specified port. If the first packet match, its expecting next one. If next packet is not the right one or the time is exhausted, it will reset the time.
3] If the knocking sequence is successful, knock daemon will add another firewall rule BEFORE the "blocking" in which will allow incoming connection on port 20202 from IP from which the correct knocking was received. This will allow SSH connection.
4] After the time is expired, or if the "closure" knocking is received, knock daemon will remove that temporary rule and the system is again "closed"
So, when the system is "closed", a full port scan will return that no SSH port is OPEN -> No way how to even try to connect via SSH
For the knocking itself, there are lot of application for windows, linux, android, iphone, MacOS, ... etc. all over the net. Check
this for example and also for detailed info about configuring the knock daemon, etc...
NOTE:
-
Port knocking is not the replacement of the security, it is just additional protection layer!!!
- It is NOT bullet proof. Best scenario is if there is no another "online" service on the system - NO port is open and system is DROPPING (instead of denying) all incoming connection. It looks like there is NOTHING interesting behind that IP. If there are another services like apache, https, etc ... It could be like "Aaaah, maybe there iiiis somethiiiing and its just hidden!"
- If the attacker is on same network like the knocker, he could sniff packets and reveal knocking sequence to pass this protection. Another danger is IP spoofing. Both of these could be eliminated by hashed port-knocking sequence.
- If the knock daemon crash, there is simple no way how to "open" the port from the outside, so some kind of monitoring which will restart the knockd in case of crash. Or another way how to access the system and restart daemon)
- In some cases the knocking sequence could arrive in wrong order or some of the packets could get lost, which will make the knocking as failed attempt.
Good thing: There is FreeBSD
knock daemon
Bad thing: It is not present in FreeNAS version.
If someone does not like the disadvantages or if he is much more paranoid, there a similar, but much more robust (and also a bit complex) way which is
SPA.
Holy